Keystroke Logging and Password Masking
Table of Contents
1. Keystroke Logging
Syteca allows keystroke logging to be enabled to assist in the detection of malicious insiders and protect your sensitive data on the endpoints. In addition, to get information only on the potentially-suspicious activities, you can enable the recording of user activity to be started automatically on detection of specific keywords typed.
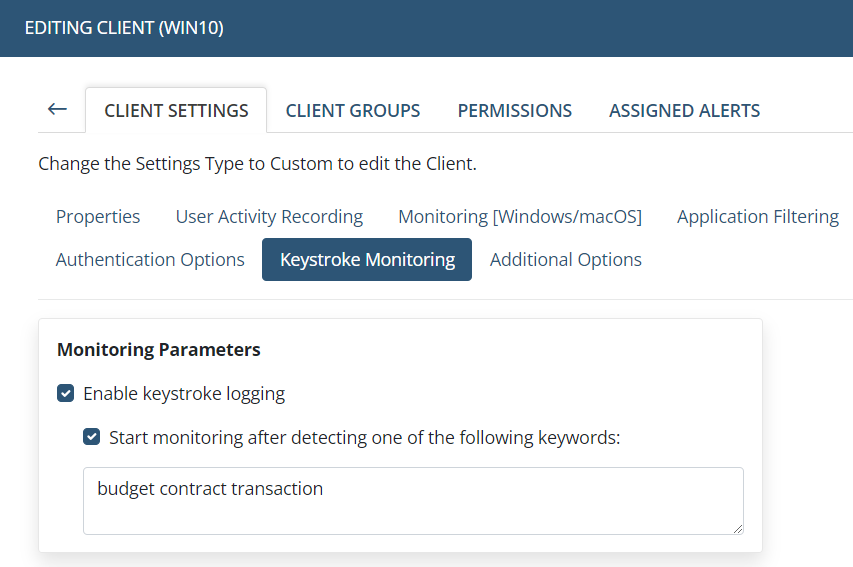
To help ensure compliance with privacy laws, standards and regulations (e.g. GDPR), all keystrokes logged are hidden in the Session Viewer and in reports, but searches can be performed on this data, and alerts can be created to be triggered when specific keywords are typed by a user.
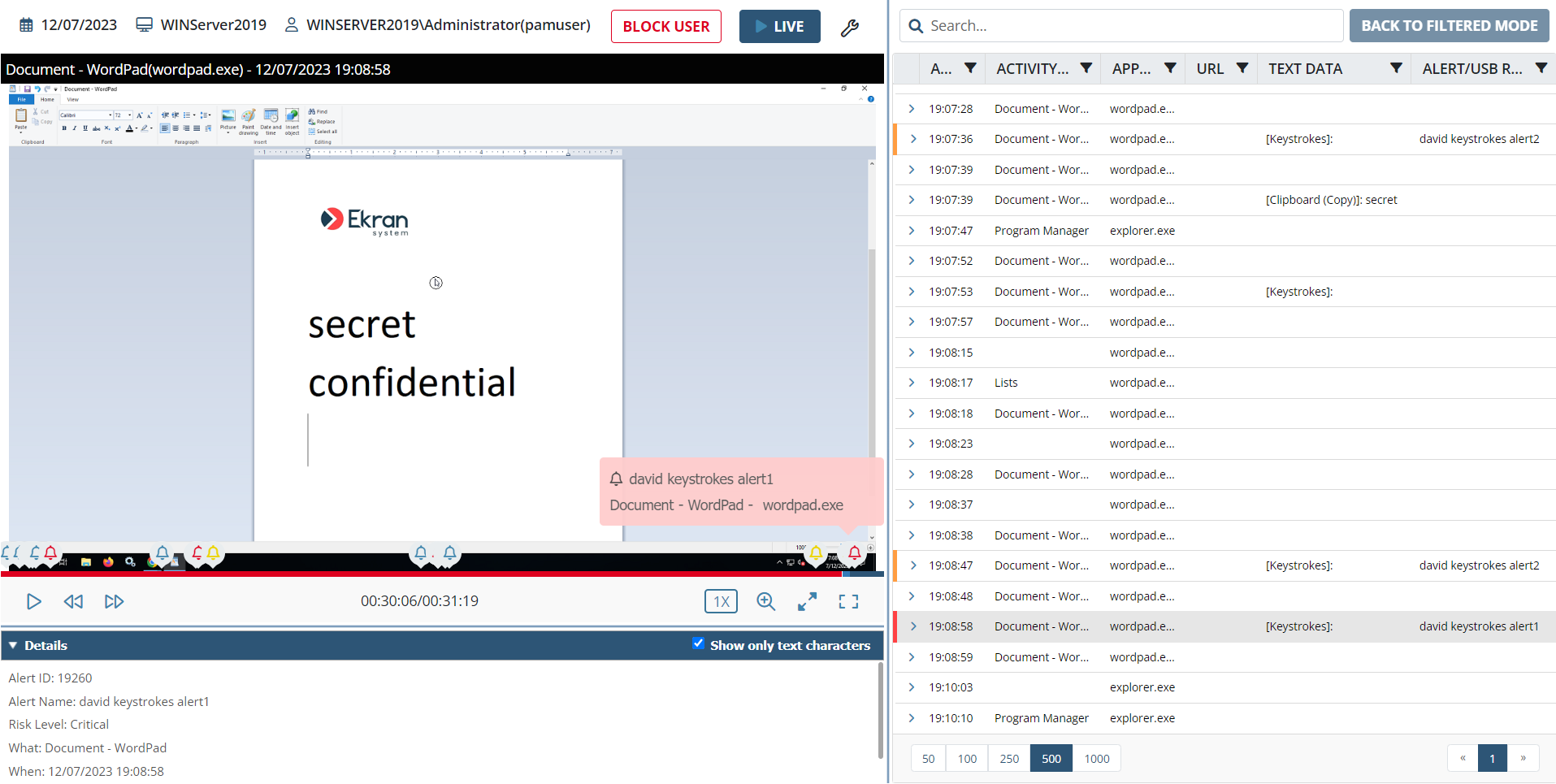
If you want to enable the displaying of keystrokes in the Session Viewer and in reports, please contact us at: https://www.syteca.com/en/support/contact-support; or send an email to: info@syteca.com
.png?inst-v=362ca448-a20b-4783-93c2-f49186888f5c)
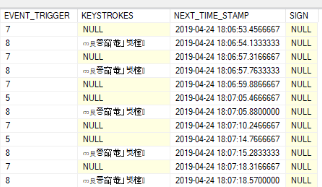
Keystrokes logged are encrypted in the MS SQL and PostgreSQL databases by the unique Syteca Master Certificate which is generated on installation. This means that persons having direct access to the database, will not be able to review the keystrokes logged.
2. Password Masking
During monitoring, the Syteca Client detects passwords using regular expression. Passwords that match regular expression are masked (i.e. hidden by replacing them) with asterisks, and are not sent to the Syteca Application Server.
.png?inst-v=362ca448-a20b-4783-93c2-f49186888f5c)
If you need to change the default regular expression to detect passwords that meet your password policy, please contact us at: https://www.syteca.com/en/support/contact-support; or send an email to: info@syteca.com
