Password Checkout
The Password Checkout functionality allows security to be enhanced primarily by preventing more than one user from using any specific secret at any given time, but also includes options for rotating the secret’s password automatically, forcing the password to be checked in by an Owner/Editor of a secret so as to log the user out of the secret immediately, etc.
So when a secret is in use by one user, no other user can use this secret, since its password is “checked out” exclusively by the current user. After a user finishes using a secret (i.e. the user disconnects or is disconnected from the account that the secret is connected to), the secret’s password is returned back to the vault, so that the secret once again becomes available for exclusive use by any user, since its password is then “checked in” again.
Furthermore, in the event of more than one person sharing the same user account credentials, the secret can still only be used exclusively by one person at any given time, and the person who used the secret can be identified.
To be able to configure the Password Checkout functionality, a user must have the Owner or Editor Role Type permission for the secret.
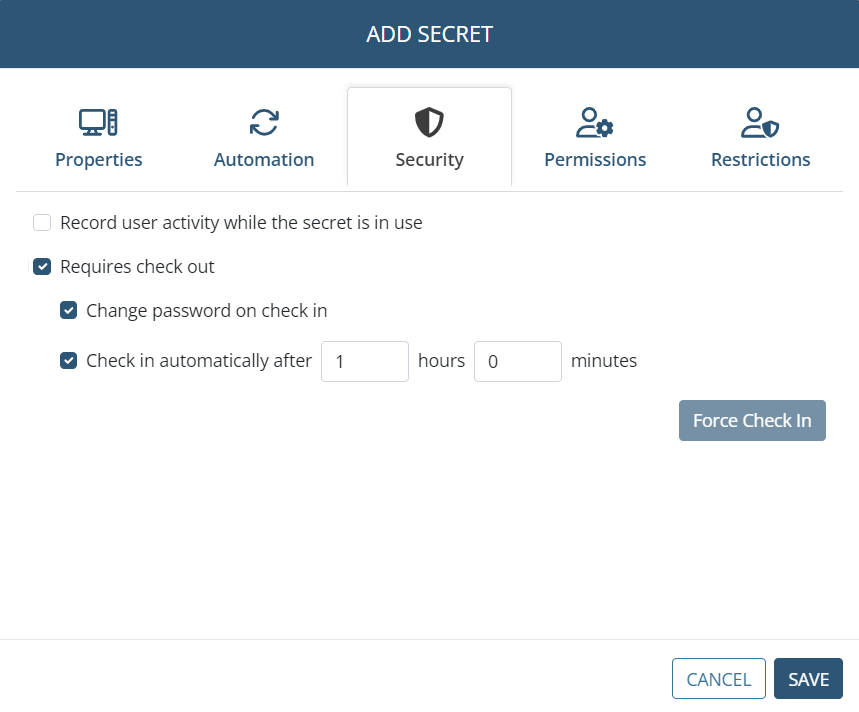
To configure the Password Checkout functionality for a secret, on the Password Management page (see below), while editing or adding a secret, on the Security tab, do the following:
• Requires check out: Select this checkbox to enable the Password Checkout functionality, so that only one user can exclusively check out the secret's password (i.e. can connect to the account that the secret connects to) at any given time.
• [For the Active Directory account, Windows account, Unix account (SSH), and MS SQL account secret types only:] Change password on check in: Select this checkbox for the password to be rotated every time the secret's password is checked back in (i.e. every time a user disconnects or is disconnected from the account that the secret is connected to).
NOTE: If the File Transfer functionality is to be used, both of the above checkboxes (i.e. "Requires check out" and "Change password on check in") must be selected, before it is possible to transfer files using the WinSCP application.
NOTE: The “Change password on check in” checkbox is completely independent of the “Enable remote password rotation” checkbox (on the Automation tab - see above), both of which can therefore function at the same time without affecting each other.
• Check in automatically after: Select this checkbox to specify a time period, after the expiry of which the secret's password will be automatically checked back in (i.e. after which the current user of the secret will be forcibly disconnected from the account that the secret is connected to).
NOTE: The “Check in automatically after” checkbox is completely independent of the “Allow access without approval during work hours” checkbox (on the Restrictions tab - see below), both of which can therefore function at the same time, in which case the user will be automatically logged off at whichever time period expires first.
• Force Check In (button): After adding the secret only, while editing it later, this button can be clicked at any time to manually check the secret's password back in (i.e. to forcibly disconnect the current user of the account that the secret is connected to) at any time.
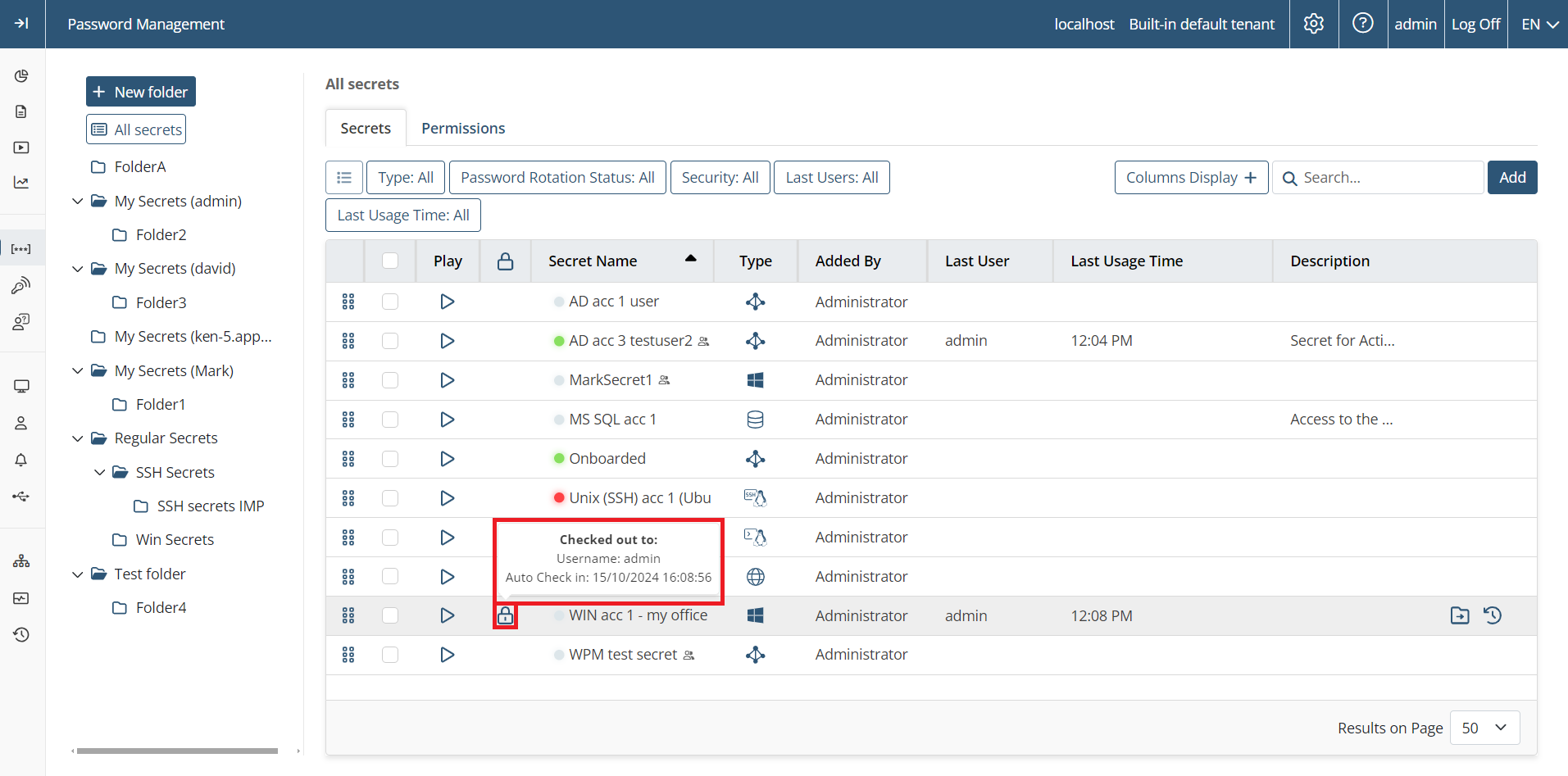
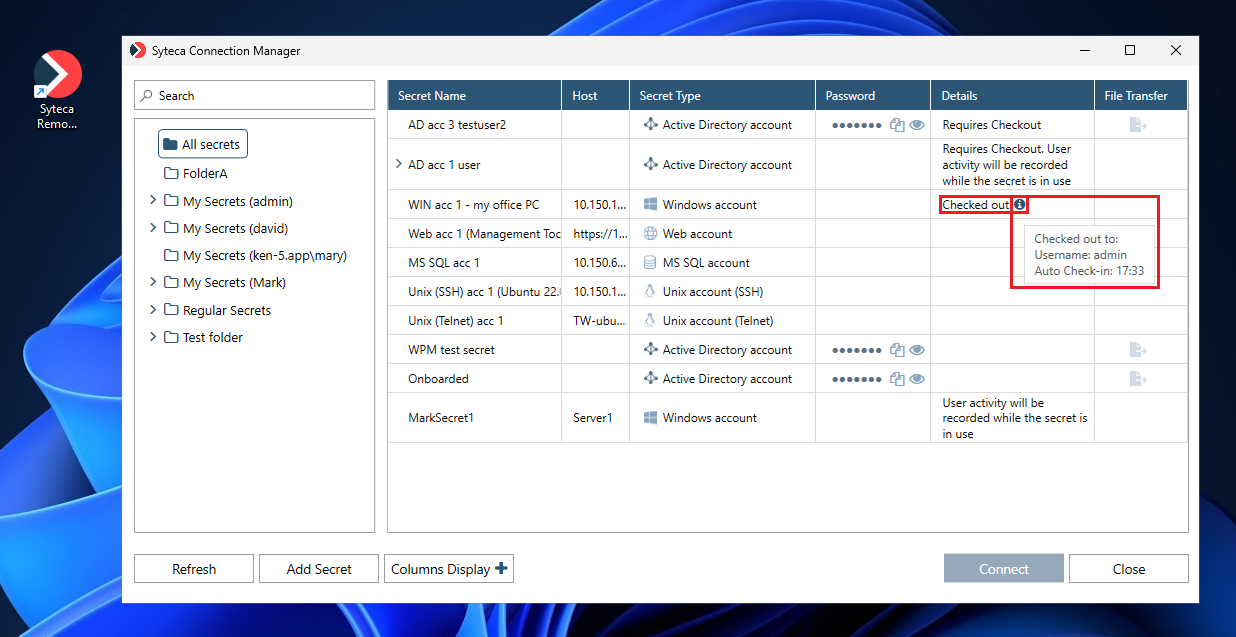
To view information about the status of the Password Checkout functionality for all secrets, do either (or both) of the following:
• Open the Password Management page (on the Secrets tab) to view the list of secrets displayed in the grid, where the Checked out (

• Open the Syteca Connection Manager to use the secrets, where the Password Checkout status (if enabled) is displayed in the Details column (and if the password in checked out, more details are displayed in the corresponding hint when hovering over the 
NOTE: The Password Checkout functionality is completely independent of the Access Approval functionality (on the Restrictions tab), both of which can therefore function at the same time, in which case the user will need to request and receive approval before they can use the secret.
